 International. As the world tries to take control over the spread of the Coronavirus and tries to contain, eliminate and prevent it from spreading, hackers around the world have found that the Coronavirus serves as an enabler for their activities.
International. As the world tries to take control over the spread of the Coronavirus and tries to contain, eliminate and prevent it from spreading, hackers around the world have found that the Coronavirus serves as an enabler for their activities.
Our latest Global Threat Index for January 2020 shows that cybercriminals are exploiting interest in the global epidemic to spread malicious activity, with several spam campaigns linked to the virus outbreak.
Viruses can be transmitted in various ways, through saliva, touch, or even through the air, and malware is similar in that it finds different vectors to penetrate.
Immediately after the huge global attention around the Coronavirus, cybercriminals began to use the interest to spread their malicious activity. The graph below shows the trend line of google Trends' overall coronavirus search, compared to the trends we observed in the social media discussions about cybersecurity and cybercrime mentioned in relation to the virus.
In January and February 2020, the most prominent campaign with the Coronavirus theme targeted Japan, distributing Emotet in malicious email attachments that purported to be sent by a Japanese provider of social assistance services for the disabled. The emails appeared to be reporting where the infection spreads in several Japanese cities, encouraging the victim to open the document for more information. When the document was opened, Emotet was downloaded to the victim's computer.
Emotet is an advanced, self-propagating and modular Trojan. It was originally a banking Trojan, but has recently been used as a distributor of other malware or malicious campaigns. It uses multiple methods to maintain persistence and evasion techniques to avoid detection. It can also spread through phishing emails containing malicious attachments or links.
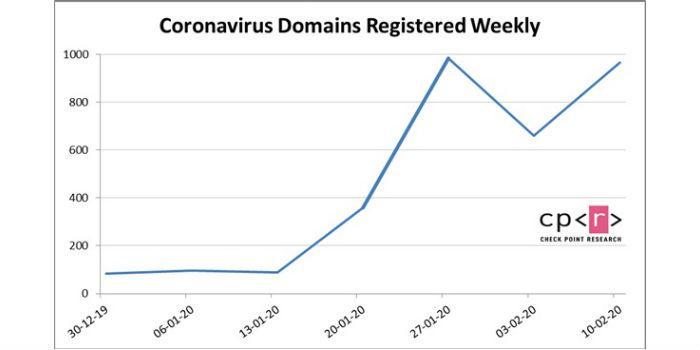
In addition to email campaigns, since the Coronavirus outbreak, we have observed a remarkable number of new websites registered with virus-related domain names (see chart below):
Many of these domains will likely be used for phishing attempts. By now, Check Point has already detected and protects online users of many websites known to be related to malicious activities that lure victims to their websites with discussions about the virus, as well as fraudulent websites that claim to sell face masks, vaccines, and home tests that can detect the virus.
An example of this website is covid-19 vaccine\.com. It was first created on February 11, 2020 and registered in Russia. The website is insecure and offers to sell "the best and fastest test for Coronavirus at the fantastic price of 19,000 Russian rubles (about US$300)."
The website also offers news and a map of the spread of the Coronavirus, but looking closely at it you can see that it is designed in an immature way, providing instructions and comments as "a place for a beautiful subtitle".
Stay protected
So how can you avoid falling victim to these scam attempts? Our recommendations for safe online behavior are:
Be sure to order products from an authentic source. One way to do this is to NOT click on promotional links in emails and instead Google the desired retailer and click on the link on google's results page.
1. Beware of "special" offers. An 80% discount on a new iPhone or "an exclusive cure for Coronavirus for $150" is usually not a reliable or reliable buying opportunity.
2. Beware of similar domains, spelling errors in emails or websites, and senders of unknown emails.
3. Protect your organization with a holistic end-to-end cyber architecture, to prevent zero-day attacks
* Report from Check Point Software Technologies.

























Leave your comment