Learn about the new scam of fake captive portals that cybercriminals use to buy streaming services with your internet account.
by Eliot Eggers*
If you live in Mexico City, you will surely have noticed that the free WiFi services of various telephone companies such as Izzi, Telmex and TotalPlay have increased considerably, causing mexico city to break the Guinness record on November 9, 2021 for presenting the impressive number of 21,500 hotspots located throughout this metropolis.
And to all this, where is the problem? These WiFi networks must be secure, shouldn't they? Well... Not exactly. The networks these companies provide are in effect usually secure most of the time. The problem is when we connect to a cloned network that is operated by cybercriminals. Wait... what? Why would anyone put a fake WiFi network near a restaurant or coffee shop? In reality there are several reasons such as trying to spy on the information we send while browsing, going to fake websites or simply stealing our access credentials with which we pay for our internet services, which is what we are going to focus on this day.
How do I create a fake WiFi network?
Certainly creating a fake WiFi network is something quite simple to do, since all an attacker needs is to have a long-range WiFi antenna (whose cost is usually low), in addition to a computer with free applications such as "Aircrack-ng" or "WiFi Pumpkin", which serve to mount a fake network from the comfort of home or a nearby café. Once this fake network is implemented, there is only one more thing to do: implement a fake captive portal.
What are wiFi captive portals and how can they be faked?
If you have ever used the WiFi network at the airport or in a hotel or café, you will have already noticed that when you connect to these public networks automatically your cell phone or computer shows a web page where you must accept the terms and conditions of use of said network to access it.

Fake WIFI Captive Portal
These web pages that appear as soon as we connect to the WiFi are known as captive portals. In them, many companies not only ask us to accept the terms and conditions of the use of the network to give us access to WiFi, but we are also requested to enter with our users of social networks, such as Facebook, Twitter or Google.
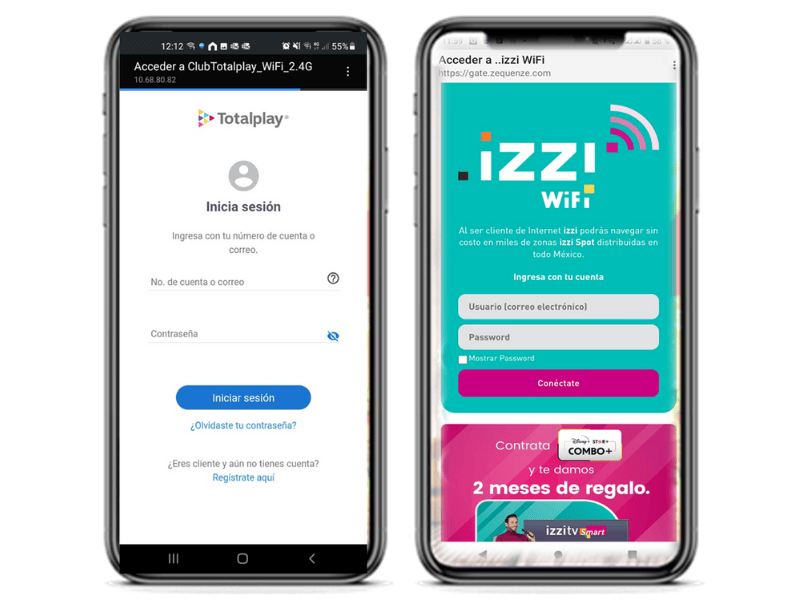 However, if you have used the services of Club TotalPlay or Izzi Spot then you will have noticed that in order to make use of these networks we must access with the same passwords with which we pay for our internet services, either from the application or website of these companies. And this is where the problem lies. Well, these captive portals can easily be cloned by a cybercriminal whose purpose is to steal our credentials.
However, if you have used the services of Club TotalPlay or Izzi Spot then you will have noticed that in order to make use of these networks we must access with the same passwords with which we pay for our internet services, either from the application or website of these companies. And this is where the problem lies. Well, these captive portals can easily be cloned by a cybercriminal whose purpose is to steal our credentials.
Discovery of fake WiFi networks
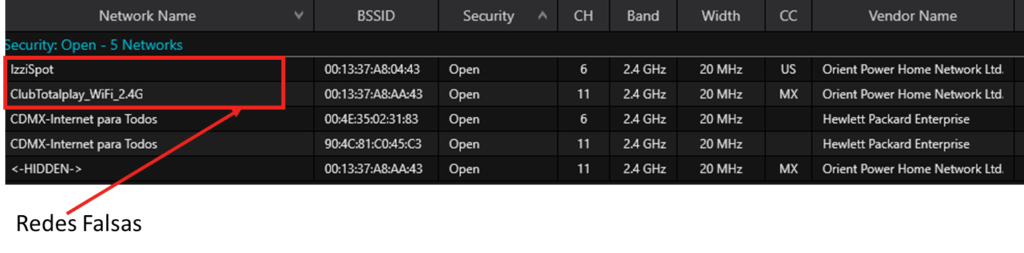
A few weeks ago, after auditing some networks in Mexico City, I found at least 15 fake WiFi networks in the center of Mexico City, which were posing as networks of Izzi, Totalplay and Telmex.
These networks were found to be fake because, when trying to enter these web pages with fake users like [email protected] with random passwords, I always gained access to the network. Being able to enter a network with fake users implies that no user authentication is being carried out by the phone companies, so it is easy to deduce that these networks were there only to obtain user credentials. Among other things that we could also notice is that the MAC addresses of these networks did not belong to any brand of commercial wifi equipment, in addition to the fact that these networks canceled their internet service shortly after connecting to them.
After a few days, inside the controlled environment laboratory, we did some tests where we replicated this attack with tools similar to those that a cybercriminal would use. And the attack worked immediately. In a matter of minutes we had already cloned the captive portals of various internet companies. However, this fake network was out of reach for any user outside the test equipment.
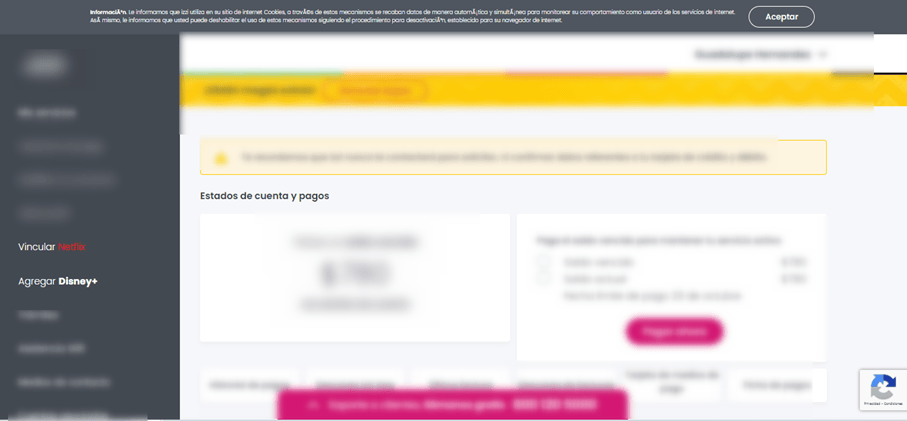
However, it should be noted that any clueless person who decided to enter a fake captive portal would grant their Izzi, TotalPlay or Telmex credentials to a cybercriminal, who could buy streaming accounts from the portals of these companies. It is only necessary that the affected user has his debit or credit card domiciled to the account, in order to start buying streaming accounts or other things that the telephone company in question allows.
And so what can we do to protect ourselves?
Here are some recommendations to avoid falling into fake WiFi network attacks:
1. Try to enter with false credentials before granting the true credentials: this is because most fake captive portals do not verify that our information is true.
2. Use our cellular data when possible: While this is not always an option, it is usually safer to use our cellular data to surf the internet. This is because in cellular networks no attacker can monitor our information without having access to our cellular equipment.
* Eliot Eggers, Ethical Hacker in Intelligent Networks.