Analysis on risk management addressed from ISO 31000 and ISO 27005, understood as a complement, not as a competence.
by Gigi Agassini, CPP*
As a security professional I believe that we are constantly facing risks, learning how to manage them, making the best decisions, talking about risks, documenting how they evolve; Know trends about what this 2023 will bring onwards and much more. I ask you dear reader: are we really making the smartest decisions to efficiently manage the risks of our companies?
The risks have a financially significant impact on companies as well as reputational damage. Analyzing and managing risks effectively allows us to prevent problems before they occur, helping us save time and money. In today's uncertain and fast-paced world, analyzing, assessing and managing risks can save the corporation a lot.
Managing risks is a fundamental part of governance and leadership, since it has traceability at all levels of the organization, from identifying activities associated with risks to constant interaction with executives. Risk management must consider the external and internal context of the organization, including human behavior and cultural factors.
There are several "frameworks" and standards for risk management and probably the obligatory question is which one is correct?
On this occasion I would like to talk about ISO 31000 and ISO 27005, since both specialize in risk management, but sometimes there is confusion about how and where to apply them.

It is important to note that they are not the same and that one does not replace the other. In the standards there is no "competition" to see which wins, as if we were in a ring watching two opponents fight between the technicians and the rough ones in a "mask vs. hair", as the vast majority of standards complement each other.
If we start from the principle that there is a physical world and a digital world that today is oneself, we do not lose sight of the fact that each one has different challenges, risks and dynamisms and, although they converge, they take care of each other differently.
Let's add to the above other relevant factors such as the type of business we have, the location or geographical locations, the size of the business, the corporate strategy, the objectives, the vision, the culture, the risk appetite, to name a few. All this will lead us to choose the standard or standards that should be implemented and complemented.
ISO 31000
It is an international risk management standard that provides principles, framework and process for risk management and can be used by any organization regardless of size, activity or sector.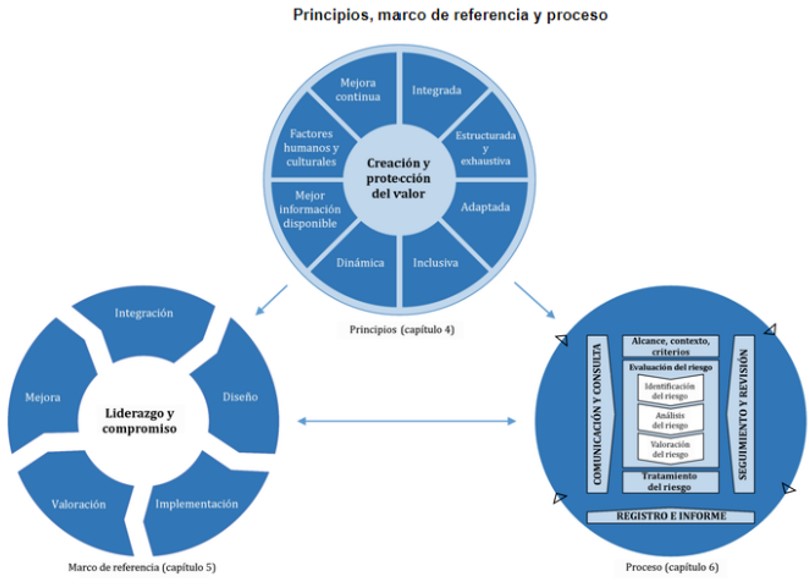
Its use can help organizations achieve objectives, improve the identification of opportunities and threats, and effectively allocate and utilize resources for risk management.
However, it cannot be used for certification purposes, but provides guidance for internal and/or external audit programs. It also provides sound principles for effective management and corporate governance for those organizations that implement it. It also has guidance on how to apply risk assessment techniques (ISO/IEC 31010), enabling organizations to better manage risks and continuously increase their value in a systematic and structured manner1 .
ISO 27005
It is an international risk management standard, specifically information security risk assessment and treatment, provides guidance on the implementation of the information security risk requirements specified in ISO/IEC 27001 and is applicable to all organizations regardless of type, size or sector.
This standard is intended for use by organizations that intend to establish and implement an Information Security Management System (ISMS) in accordance with ISO/IEC 27001. It is aimed at people involved in information security risk management and organizations that intend to improve their related management process.
It states that risk management best practices should be defined according to the characteristics of the organization, taking into account the scope of its ISMS, the risk management context, as well as its industry. It also provides guidance on the implementation of the ISO 31000 risk management guide in the context of information security. The standard contains detailed guidance on risk management and complements the ISO/ICE 270032 guide.
To talk about risks, the first thing you need to do is take risk seriously.
Although risk management should be a central element of any information security strategy, today it is not a well-understood or widely used discipline, although awareness of its importance is beginning to increase, we are still far away.
It is very common for risk records to be put in complex and non-concise language, it is important to place them in the language of the business and not in technical language, as well as to properly point out the potential impacts on the commercial operations of the business. Let's not lose sight of the fact that every business has two measures: sale and loss.
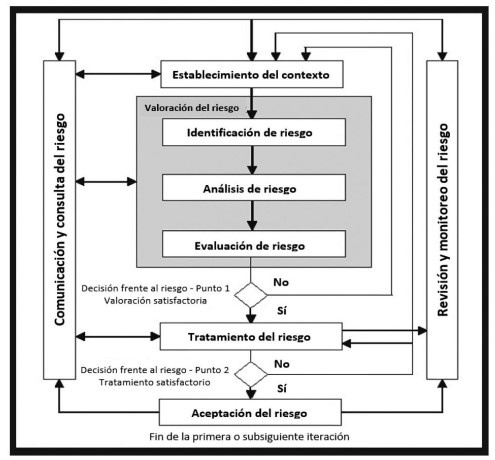
Risk management best practices have been developed over time to meet specific needs in various industries through the use of different methodologies, and ISO 31000 is the matrix standard that provides the guidelines and general principles to manage any type of risk in a systematic, transparent and reliable manner, while ISO 27005 is the specialized standard that complements the matrix by providing best practices to manage Risks related to information security.
I leave you this great reflection of Nassim Nicholas Taleb from his risk book, "The Black Swan" where he wrote: "Our problem is not only that we do not know the future, we also do not know much about the past."
Managing new risks and weaknesses is, or should be, the goal of risk management.
Until next time!  * Gigi Agassini, CPP
* Gigi Agassini, CPP
International Security Consultant
GA Advisory
[email protected]


























Leave your comment