 International. A few days ago, Ankit Anubhav, Principal Investigator at NewSky Security, revealed on Twitter that login passwords for tens of thousands of Dahua DVRs have been cached and indexed by IoT search engine ZoomEye. To make matters worse, this vulnerability, CVE-2013-6117, was initially discovered in 2013 with a firmware patch subsequently released by the company to fix it.
International. A few days ago, Ankit Anubhav, Principal Investigator at NewSky Security, revealed on Twitter that login passwords for tens of thousands of Dahua DVRs have been cached and indexed by IoT search engine ZoomEye. To make matters worse, this vulnerability, CVE-2013-6117, was initially discovered in 2013 with a firmware patch subsequently released by the company to fix it.
Despite numerous warnings from cybersecurity experts in recent years about the importance of patching IP physical security equipment against known vulnerabilities, it appears that that message has yet to be consolidated in some corners of the industry.
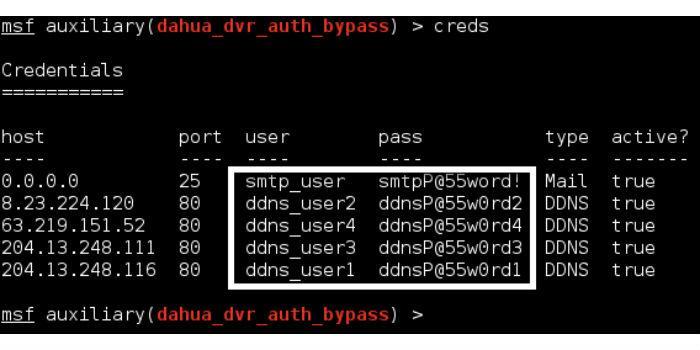
Last week, Ankit Anubhav, Principal Investigator at NewSky Security, revealed on Twitter that login passwords for tens of thousands of Dahua DVRs have been cached and indexed by IoT search engine ZoomEye. To make matters worse, this vulnerability, CVE-2013-6117, was initially discovered in 2013 with a firmware patch subsequently released by the company to fix it.
Even though they stopped their investigation after discovering the extent of the vulnerability and couldn't really say how many had already been compromised by the hackers, Scott Wu, co-founder and CEO of NewSky Security, which has a number of customers with enterprise IP camera systems in the Smart Cities and Smart Buildings sectors – says the potential impact for owners of these devices is obvious and that many of them are they are already "owned" by malicious actors or have a "critical risk" of being owned. In fact, Wu says he'd be surprised if not everyone is already engaged, considering how fast information moves in the underground Internet economy.
"It's a vulnerability of the DVR, which responds to querying credentials in plain text," Wu explains. "ZoomEye, as an IoT search engine similar to Shodan, stores and indexes search results, including credentials unfortunately given through the vulnerability."
For its part, Dahua issued a statement a few days ago asking the owners of the affected devices to update them and change their passwords. "We note that some media outlets recently reported on CVE-2013-6117, which was resolved in 2013. We strongly recommend customers using DVR versions before 2013 to update the device and change the password. The latest firmware can be downloaded from Dahua's website," the statement reads.
Dahua also encouraged everyone who has cybersecurity-related questions to contact the company via email at [email protected]

























Leave your comment