 Latin America. The A3SEC Digital Security and Surveillance Center has been alerted to a massive ransomware attack against several companies, which consists of exploiting a vulnerability published by Microsoft on April 14, 2017, allowing code execution remotely if a manipulated message is sent to the SMBv1 service. Kaspersky, a Russian computer security company, estimated more than 45,000 cyberattacks perpetrated by ransomware-type viruses.
Latin America. The A3SEC Digital Security and Surveillance Center has been alerted to a massive ransomware attack against several companies, which consists of exploiting a vulnerability published by Microsoft on April 14, 2017, allowing code execution remotely if a manipulated message is sent to the SMBv1 service. Kaspersky, a Russian computer security company, estimated more than 45,000 cyberattacks perpetrated by ransomware-type viruses.
"Attackers are encrypting computer information with outdated operating systems. They have the possibility of violating these computers by hijacking the information and when the user wants to access with their data, in exchange they are asked for a sum of money in bitcoins, "says Jorge Imues, director of operations of the A3SEC Group.
The detected cyber attack was categorized at the "very high" alert level massively affecting companies worldwide. Some of the affected systems are:
- • Microsoft Windows Vista SP2
- • Windows Vista x64 Edition Service Pack 2
- • Windows Server 2008 for 32-bit Systems Service Pack 2
- • Windows Server 2008 for x64-based Systems Service Pack 2
- • Windows 7 for 32-bit Systems Service Pack 1
- • Windows 7 for x64-based Systems Service Pack 1
- • Windows Server 2008 R2 for x64-based Systems Service Pack 1
- • Windows Server 2008 R2 for Itanium-based Systems Service Pack 1
- • Windows 8.1 for 32-bit Systems
- • Windows 8.1 for x64-based Systems
- • Windows RT 8.1
- • Windows Server 2012 and R2
- • Windows 10
- • Windows Server 2016
Recommended actions by experts
Update 15-05-2017: Although at this moment the Ransonware WannaCry campaign was already controlled, thanks to the action of MalwareTech (a malware analyst), who managed to divert the traffic of the compromised computers to a group of servers dedicated to capturing malicious traffic and preventing the control of infected computers, we must bear in mind that the EternalBlue/DloublePulse exploits that gave rise to this attack are still publicly accessible.
In Colombia there are around 800 computers concentrated mainly in Bogotá, Medellín, Pereira, Cali and Bucaramanga with the SMB service exposed on the Internet and that could be attacked if they do not apply the security patches published by Microsoft.
According to recent notifications, Microsoft included Windows XP within the platforms with a patch for this vulnerability, an operating system still used by some users and that had run out of updates since April 2014.
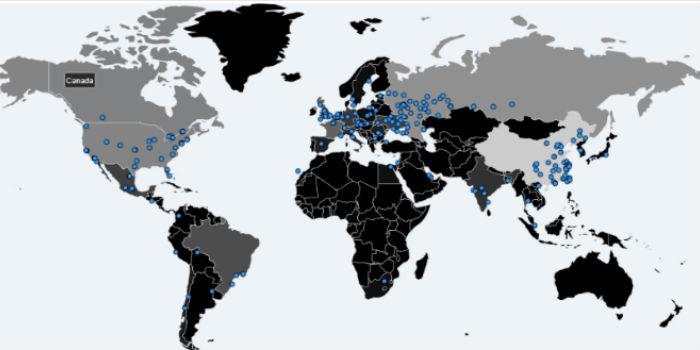
According to the current map of infections, there are only 623 compromised computers that report activity.
These are some of the recommendations provided by Jorge Imues, director of operations of the A3SEC Group, to all organizations that manage Windows operating systems and some precautions that must be taken, in order not to continue putting valuable information at risk.
• Identify if there are vulnerable computers with InsightVM (aka Nexpose) using the signature CVE- 2017-0143 MS17-010 SMB RCE Detection. Additionally, validate the public segment to identify exposed SMB services. You can download a trial version of InsightVM from https://www.rapid7.com/products/insightvm/download/virtual-appliance/, in OVA format, and then mount it on any virtualization system, including Virtualbox. You will receive in your mail a serial for the trial period.
• Install bulletin MS17-010 (Kb 4013389) on vulnerable computers.
• Filter the exposed SMB services in the perimeter firewall.
• If your antivirus has the ability to identify malicious files by hash, scan all endpoints and servers for the following hash and quarantine it: b9c5d4339809e0ad9a00d4d3dd26fdf44a32819a54abf846bb9b560d81391c25.
• If you have already been a victim of the attack stay updated through social networks on the advances that there are to solve the problem, many security companies are joining forces through the project www.NoMoreRansom.org #nomoreransom and keep updated the CRYPTO SHERIFF application to decrypt files hijacked by Ransomware.
• Update your antivirus and deploy a mass scan, make sure beforehand that the manufacturer already has a signature to detect it.
CN-CERT has developed an application that prevents the execution of the WannaCry Ransomware, it should only be mentioned that the application should run after each system reboot: https://loreto.ccn-cert.cni.es/index.php/s/tYxMah1T7x7FhND

























Leave your comment