The Video Management System (VMS) offers strategic benefits for security management. That is why it is unthinkable, for certain verticals, the installation of CCTV without this management solution, which delivers innovative alternatives, as well as technological resilience.
Iris Montoya Ricaurte
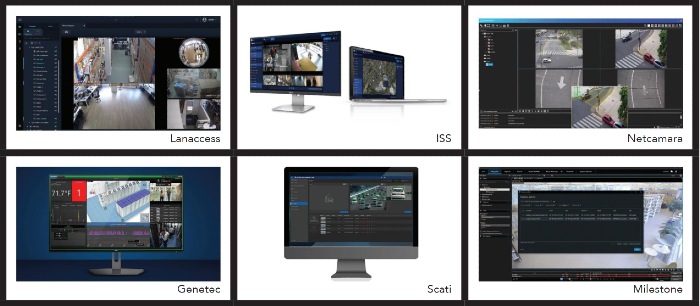
As Miguel Gimeno, Business Development & Marketing Director at Scati, explains, VMS have been adapting and developing for years at the pace of new technologies, while their use is democratizing and extending.
 In that sense, the implementation of Artificial Intelligence (AI), cloud-computing, IoT and cybersecurity are being rapidly driven in these solutions, which have also appropriated Big Data and Business Intelligence.
In that sense, the implementation of Artificial Intelligence (AI), cloud-computing, IoT and cybersecurity are being rapidly driven in these solutions, which have also appropriated Big Data and Business Intelligence.
For Gimeno the VMS "is converging on a unified management platform to increase collaboration and help management make better decisions, based on more complete data and analysis. There are several actors who are focusing on the VMS as a VSaaS, but this type of operation will depend a lot on the particular conditions of each user".
While this is an interesting trend, as it requires innovation from manufacturers, not all VMS that are on the market have this approach and versatility in their operation. Hence, it is worth understanding what are the characteristics of an ideal Video Management System.
Characteristics of a good VMS
In the words of Juan Guillermo Gómez, Regional Sales Manager for Colombia and Ecuador at ISS (Intelligent Security Systems), a VMS empowers three things: first, "make the most of the peripherals they implement in the system". Second, "ensure the availability, confidentiality and integrity of the data it handles." And third, but not least, automate security processes.

The latter means that, as a tool, its job is to facilitate the work of those who use it. "Allow, through alarms, messages, a friendly user interface, analytics and interaction with other subsystems, to focus attention on important events and, from the real management of the video, to improve the efficiency of the operation, without depending 100% on human intervention."
Gimeno ensures that when choosing a VMS it is sought to be open, scalable, secure and easy to use. "It has to serve properly, both for large facilities projects and for smaller and distributed ones. In addition to being able to centrally configure the entire CCTV platform, efficiently monitor images in real time and receive alarms from the video system, as well as being open to integrations with other security systems."
At the physical level, the expert said that it is desirable to have the hardware redundant in 'failover' mode, because this "will give a plus of reliability" and, in the same way, the installation of this hardware must be carried out "in adequate and controlled environments for its uninterrupted operation 24x7".

For his part, Gustavo Battista, commercial and marketing director for Latin America at Netcamara, counts as three areas in which a VMS responds. From the administrative level, limit access and extraction of information to accredited users. Security must have basic functionalities, such as detecting people or activity in restricted areas or times. And, from the operational point of view, it has a call to "facilitate access to information and the results that it processes in an automated way."

In addition to this, Daniel Llanas, Commercial Director for Latam at Lanaccess, considers that a good VMS gives the option of connecting to a streaming server, for access by remote users. "This is useful, for example, for banks connected to law enforcement." Similarly, this engineer suggests integration with other devices, such as access control, a desirable matter to mitigate additional security risks.
Regarding this integration with other devices, Camilo Sánchez, Business Development Manager at Genetec, indicated that, because in the current market there are very advanced camcorders, the idea is to be able to exploit to the maximum the features offered from the VMS.
Therefore, for Sánchez an ideal VMS "is flexible to the needs of the client and scalable. So that it can start in a certain number of cameras and grow. More now that many projects are done in phases. Also, because end users have their own growth rate, including migrations from analog technology."
The Genetec specialist added that we should not lose sight of cybersecurity requirements, especially when today all the actors involved in the choice, installation and operation of security solutions are responsible, "manufacturers, integrators and end users must increase that awareness".

In this regard, his recommendation is "to work with manufacturers committed to this issue and that have standards that support it, such as UL 2900. This is evidence that there is a third party that is certifying the performance and ability of the software, in this case the VMS, to protect itself."
Against limitations and vulnerabilities
However, failures are not alien to these systems, especially if you take into account that they are products that improve over time and add functionalities.
Israel Austria, Milestone Systems solutions engineer for Latin America, explained that VMS, like any other type of system, is not exempt from a certain level of failure. "Along with the developers of new methodologies and procedures in cybersecurity, those who seek to find the vulnerabilities of these work and, on the other hand, we have the human factor, where no matter how sophisticated a security tool may be, if it is not well implemented or omitted, it will open the possibility of incidents occurring."
Gustavo Battista agrees that these disadvantages "are usually associated with the human factor, such as negligence in terms of configuration, protection of credentials or the incorrect parameterization of events and alerts, which are then ignored by operators."
While Juan Guillermo Gómez was inclined to explain the limitations that VMS may have, from two large groups, on the one hand the 'monobrand', those that are developed by the same manufacturer of the peripherals, and on the other those that are open.
For the first case, "the interoperability between the VMS and the peripheral devices of the same manufacturer are integrated natively and therefore their operation is usually more "transparent" for implementation and configuration. However, when the customer wishes to interoperate with equipment of different brands, there are quite marked limitations, or even incompatibilities, mostly of a commercial nature."
That is, more directly integrating camcorders and VMS with third parties would reduce the competitive advantage of the portfolio. Hence, many manufacturers prefer to focus the advantages on their own devices, added to the guarantee of handling protocols and encryption in the same languages.

In the second scenario, when VMS are open or developed by brands whose portfolio does not focus on peripherals, "the main limitation is because the standards, which seek to homogenize support between open VMS and cameras, do not go at the same speed as the development of functions that peripheral manufacturers have."
Another point regarding vulnerabilities was exposed by Glenn Patrizio, president of LAR for Latin America and brand representative, who explained that it is unlikely that a VMS suffers a cyberattack, but not impossible, and that when it happens it is usually through cameras. Glenn pointed out that this happens due to the lack of knowledge and caution of users, since there is a lot of online and updated information about the terminals that have these failures.
Likewise, he pointed out that the lack of software update generates the greatest gaps in operability. "Updates improve cybersecurity and performance, so it's extremely important that they are done every 4 months." The same idea was put forward by Daniel Llanas, who stated that "although these devices are not usually the ultimate target of cybercrime, they can act as the gateway for cyberattacks on corporate networks."
When a VMS solution is underutilized
Obviously, since failures are usually associated with the human factor, in the same way the waste of the benefits of a Video Management System is marked by the behavior or omissions of the end user.
For Battista "the lack of communication between the different internal potential clients of the organizations means that the benefit for the different functional areas is unknown. For example, when the VMS is driven only by security units, it often happens that areas related to customer management, marketing and others never know that they can take advantage of this system."

Israel Austria is aiming for something similar. Well, it states that different users are unaware of the different types of functions offered by their systems and that they are underutilizing. It is also the case that they do not know that they have certain characteristics. This phenomenon emerges "from the way in which manufacturers approach their potential users and their effort to communicate their offer."

Glenn Patrizio reported that another waste is that, although several VMS sell a complete solution, with access control, AI cameras and other devices, they do not take advantage of the integrations they offer. This is again the matter of the end user, who has the responsibility of finding a VMS that captures all their security needs and is integrated. "So you don't have to change all the peripherals you already have and you can take advantage of your operational capabilities."

Resilience, from added value to requirement
Technological resilience was defined by the Department of Audiovisual Engineering and Communications of the Polytechnic University of Madrid as "a return to a responsible and sustainable development and consumption of technology". Meanwhile, Rebeca Sosa García, a research professor at the Autonomous University of the State of Hidalgo, points out that as a definition in technological systems, resilience is "the ability of a system to withstand and recover from disasters and disturbances."
Both definitions indicate that VMSs must overcome attacks with as little damage as possible, as well as develop continuous improvement strategies. Not in vain is a quality that is moving from being desirable to indispensable, especially in technological solutions for industrial environments and critical infrastructures.
In this context, Gómez indicated that "any technological solution and even more, one focused on security, must strengthen and improve its evolution processes in such a way that they allow it, not only to overcome the challenges, but to anticipate them and thus provide solutions that help prevent, both the inconveniences that arise in the operation of the system, as in the day to day of those who use these technological solutions".
Austria sees the importance of resilience in VMS from two points of view. First, as a component of your system, because being a solution that delivers reliability is expected to remain operational despite the problems you face. Second, resilience as a product, being an option that delivers confidence to users, from a solid position within its market, through a good product and trade strategy.
Finally, as suggested by the representative of Milestone, the capabilities of intelligent content analysis and the possibilities of AI applications, should be the trend that VMS systems follow, since it is a substantial boost to their primary function, video management, and a better exploitation of what can be obtained from this solution, as it increases the efficiency obtained and, therefore, fully justifies the investment that could initially entail.

VMS Market Projection
According to research firm Technavio "the market share of video management software is expected to increase by $11.92 billion between 2021 and 2026, and the market growth momentum is expected to accelerate to a CAGR of 22.62%." With the characteristic that 41% of the growth will originate in America, Europe, Africa, and the Asia-Pacific region.
Likewise, the report "Video Management Software Market by End User and Geography: Forecast and Analysis 2022-2026" ensures that two factors have particularly driven the growing demand for VMS. On the one hand, the offer of video surveillance with devices connected to IoT that allow real-time analysis and decision making; on the other, the emergence of smart cities that demand these technologies.
For its part, Vantage Market Research coincided almost in the same figure, in terms of the compound annual growth rate (CAGR) as it projected 22.7%. But in general terms he pointed to higher values. He assured that this market, valued at 9.8 billion USD in the year 2021, "is projected to reach a value of 33.4 billion USD by the year 2028".

























Leave your comment