This technology has become relevant to recognize suspicious subjects and offer contactless access control. However, it has a panel of detractors that ensures it makes unauthorized image records.
By Iris Montoya Ricaurte
Facial recognition was born between 1964 and 1966, when Woodrow Wilson Bledsoe, conducted a series of investigations to confirm whether it was possible for computers to recognize human faces. In the process he considered that the intensity and angle of illumination were a challenge to achieve an efficient recording, factors that still persist.

This project called: "A human-machine facial recognition system: some preliminary results", extracted the coordinates of a set of facial features, such as the center of the pupils, the beginning of the hairline, the inner and outer corner of the eyes, among others, which were used to calculate a list of 20 distances between the various elements of the face. Data that, today, make up the basis of most of the software dedicated to offering this service.
According to the latest research on the facial detection market from MarketsandMarkets Research, it forecast a growth of 17.1% from 2020 to 2021, in which it would reach USD 4.5 billion. It also established as the main causes the increase in government spending on public security, along with the increase in the demand for contactless identity verification systems due to the impact of Covid 19.
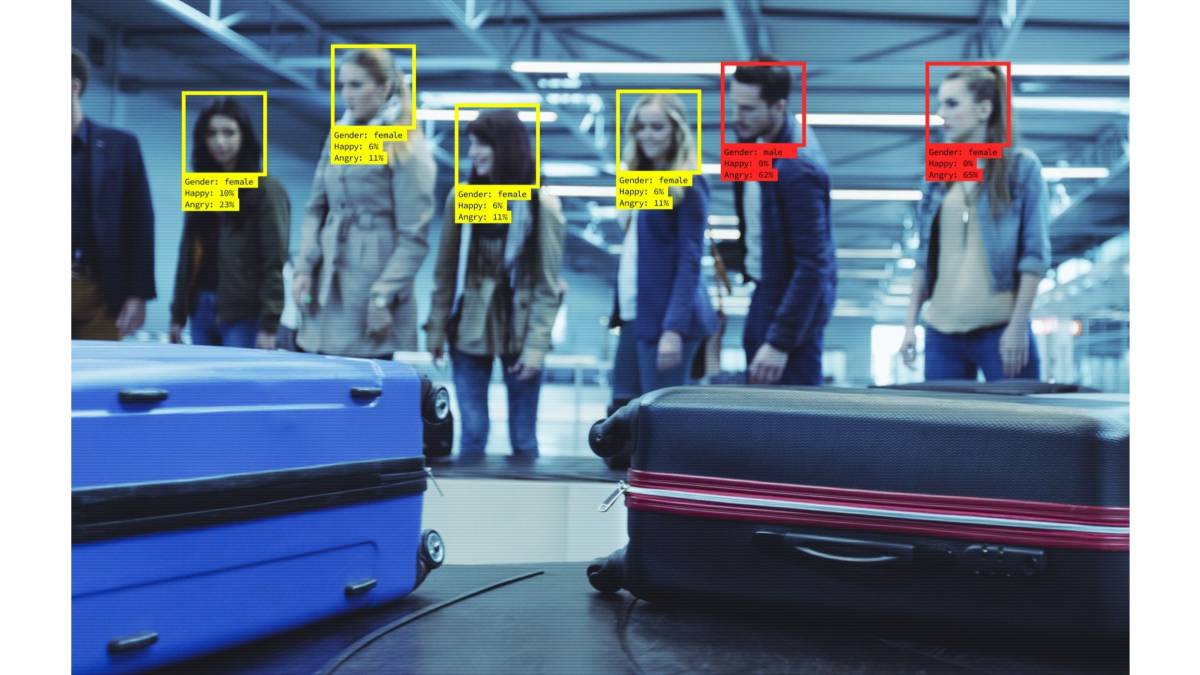
Advantages and uses of facial recognition technology For Fernando Domínguez, sales director at Herta, the benefits of this technology can be classified by verticals, where its implementation for security in transport systems, such as airports and metro stations, control operational points by the authorities; at border control, where the rigorous identification of persons is required; the retail sector, since they are usually a frequent target of common crime, and sports spaces, to avoid incidents of vandalism or actions that threaten human life.
For Fernando Domínguez, sales director at Herta, the benefits of this technology can be classified by verticals, where its implementation for security in transport systems, such as airports and metro stations, control operational points by the authorities; at border control, where the rigorous identification of persons is required; the retail sector, since they are usually a frequent target of common crime, and sports spaces, to avoid incidents of vandalism or actions that threaten human life.
 Joel Milan, representative for Latin America in SAFR of RealNetworks, assures that facial recognition has around 30 uses in the case of banking, as a tool to identify identity theft, assaults and theft to the elderly. On the other hand, it highlights its use in the monitoring of suspicious behavior in public and commercial establishments. He also adds that "it is a technology widely used in the 'customer jorney' and to improve loyalty programs in purchases."
Joel Milan, representative for Latin America in SAFR of RealNetworks, assures that facial recognition has around 30 uses in the case of banking, as a tool to identify identity theft, assaults and theft to the elderly. On the other hand, it highlights its use in the monitoring of suspicious behavior in public and commercial establishments. He also adds that "it is a technology widely used in the 'customer jorney' and to improve loyalty programs in purchases."
 In that same sense, Luis Alberto Delgado, regional director of Intelligent Security Systems - ISS indicates that "just as there are some uses of blacklists, to distinguish and track people who have already been reported or reported for various crimes, it is also concerned in customer service departments, because it helps identify the buyer and offer services according to their age, tastes and frequency of consumption. When a face is detected, for these cases, information is accessed to provide a better experience."
In that same sense, Luis Alberto Delgado, regional director of Intelligent Security Systems - ISS indicates that "just as there are some uses of blacklists, to distinguish and track people who have already been reported or reported for various crimes, it is also concerned in customer service departments, because it helps identify the buyer and offer services according to their age, tastes and frequency of consumption. When a face is detected, for these cases, information is accessed to provide a better experience."
 However, Fernando Loret, commercial director of SIASA, comments that "the application that has had the greatest boom in recent years is attendance control, because the pandemic generated that it seeks to avoid what implies an unnecessary contact. So in many cases it was passed from the use of the fingerprint to facial identification. As well as for the verification of the use of masks." Additionally, there is also its use in road safety devices, where it is used to prevent accidents by analyzing the driver's behavior and sending alerts when detecting fatigue.
However, Fernando Loret, commercial director of SIASA, comments that "the application that has had the greatest boom in recent years is attendance control, because the pandemic generated that it seeks to avoid what implies an unnecessary contact. So in many cases it was passed from the use of the fingerprint to facial identification. As well as for the verification of the use of masks." Additionally, there is also its use in road safety devices, where it is used to prevent accidents by analyzing the driver's behavior and sending alerts when detecting fatigue.
Makeup, art and resistance against facial detection
In contrast, while several researchers have focused on giving rigor and scope to facial detection, other groups have looked for ways to sabotage this potential, considering it a dangerous tool of social control.
In 2017, the Russian Grigori Bakunov, director of technological distribution at Yandex, proposed an algorithm to hide the identity with the help of makeup and said he did not want to make it commercial because of its potential to help those who should not.
This idea did not stop there, from 2019 to 2021 a group of artists generated a collaboration to explore surveillance in public space, as a result The Dazzle Club movement was born, which had proposals for makeup and clothing design focused on preventing facial recognition, as well as "silent walks" through specific areas of the city of London, designed to "subvert surveillance".
These possibilities were recently confirmed with the Dodging Attack Using Carefully Crafted Natural Makeup study, conducted by researchers at Israel's Ben-Gurion University of the Negev and published in September 2021. Specifically, they performed contradictory machine learning (AML) attacks, in the ArcFace facial recognition model, using makeup with "natural effect" on key parts of the face. This research showed that the system only managed to identify participants in 1.22% of the frames. But these types of attacks do not work at this rate of success with all systems, much less with access control, where there is a clear record in advance.
Controversy as a factor for improvement
The focus of the discussion has focused on the unauthorized existence of people's frames and records. For Luis Alberto it is clear that "the software does not take an image of the face as such, which is what most worries people, what it does is build a 'word' or vector, which is a translation of facial features into ones and zeros. So this dispute is an opportunity to encourage training for end users in the management of these tools, so that they understand how it works and close the biases that hinder the massification of these solutions."

Meanwhile, Fernando sees technology as learning and constant improvement. For him, disagreements are transformed into improvements. "From Herta we are very happy that, more and more frequently, the user guides are being implemented, which help to avoid problems derived from disinformation. There will always be those who see technology and privacy as enemies, but avoiding risks that conflict the lives of citizens must be paramount for any government and, in that sense, facial recognition is just one more tool, because the main thing is to have the ability to act and avoid catastrophes. "
For his part, Joel says that the most controversial thing has to do with the abusive use of data, which is also due to the vulnerabilities of storage platforms, where the indicated thing is that the statistics are strictly kept. "In fact, these controversies have caused systems to focus on making more responsible use of metadata. The right thing to do is to stick to local and international laws, which state: 'Don't keep more than you need.'"
 In relation to that, Nicolás Gallo, sales manager for Latin America and the Southern Cone at CDVI, considers that "companies today have greater cybersecurity implementations for biometric information, because they seek to prevent unauthorized access and theft of this data. Contrary to games and filters on social networks that make facial records without it being clear where or how they can be stored. Those are the unsafe uses that we have most at hand and that should be avoided because they expose people." To the latter can be added a contribution from Loret, who indicates that "the facial unlocking of cell phones is not a security product, but is rather a consumer product."
In relation to that, Nicolás Gallo, sales manager for Latin America and the Southern Cone at CDVI, considers that "companies today have greater cybersecurity implementations for biometric information, because they seek to prevent unauthorized access and theft of this data. Contrary to games and filters on social networks that make facial records without it being clear where or how they can be stored. Those are the unsafe uses that we have most at hand and that should be avoided because they expose people." To the latter can be added a contribution from Loret, who indicates that "the facial unlocking of cell phones is not a security product, but is rather a consumer product."
Disadvantages and difficulties of facial detection
Regarding this type of development, Luis Alberto considers as an inconvenience the unforeseen costs associated with processing, which depend on the scenarios where you want to do the installation and the type of camera that is required. "In laboratory conditions it is simple because there is total control, but in open and public spaces the conditions surrounding the equipment are not completely dominated." And he adds that this is why it is vital to verify if the offer meets the requirements. "Paper holds everything, so the invitation to those interested in acquiring these solutions is to confirm the level of reliability and effectiveness of this technology with proofs of concept (POC) prior to the final purchase."
Similarly, for Loret there are factory conditions that must be reviewed, such as the percentages of false acceptance and false rejection, "they are not 100% reliable, in addition to choosing very well the system to install, what is often done to increase that factor of certainty is to combine with other biometric data or cards, which raises the level of security". Additionally, he indicated that these solutions present difficulties in scanning people with high melanin load (dark skin) and that "because the cameras project an infrared light to measure the features, they have difficulty operating when the reading must be done under intense sunlight."
Finally, Nicolás believes that at some point the high costs discouraged the acquisition of facial detection devices, but that now with the massification of these technologies a cost reduction will be achieved in the medium to long term. Meanwhile, it does see as a disadvantage the ignorance on the part of the interested parties, who do not know how it works and how this solution should be implemented. "In fact, there are products that can expose people's biometric data, so it is necessary to socialize the knowledge of this technology, not only for companies, but also for integrators and governments."
Will there be a final verdict on facial detection?
In short, the dispute around the invasion of privacy that may or may not be exercised by devices with facial detection will remain in force and does not have an absolute answer, because it is not possible to eradicate all the variables that cause discontent to citizens, such as local regulations, the type of government exercised in your country, the ignorance, the methods of data storage by the systems and the usability that is given, as well as the advantages it has cannot be ignored.
Perhaps, the complexity of the matter is that, while there are people who prefer possibilities such as accessing their devices with their face and having CCTV in the areas they frequent, there are also interested individuals to have greater control and reserve over access to their information by organizations. But in a globalized world, where various interactions require confirming personal identity, whose strategy is to rely on technologies to generate reliable records and automate processes, the search for anonymity becomes an odyssey almost impossible to achieve.
Finally, technology has been a tool that humanity has used, both for well-being and for war, such is the case of the Internet, to give an example. So, there is no possible verdict at the moment, other than the harm or benefit does not come from facial recognition technology 'per se'.
To highlight...
Partial facial detection, by gender and skin color
Due to the pandemic we experienced a high demand for devices to help facilitate contactless entry to various facilities. That is why partial facial detection was promoted, which seeks to identify people with the mask on.

In 2020, the U.S. National Institute of Standards and Technology (NIST) examined 89 major commercial facial recognition algorithms and found that they showed error rates of between 5% and 50% when comparing photos of the same person with and without a mask. By May 2021, according to the research of the Tecnológico de Estudios Superiores de Jocotitlán, Automatic detection of faces with a mask or without a mask to restrict access to an educational institution, it was possible to develop a system capable of detecting with a 96% success the majority of the people scanned, but it resolved that a system of this type was complex to operate in environments with lighting problems and ambiguous backgrounds.
Another concern has been to pluralize the ethnic traits detected by this technology. In 2018 Joy Adowaa Buolamwini, researcher at the MIT Media Lab and founder of the Algorithmic Justice League, led a study where bias was identified in datasets and automated facial analysis algorithms in 3 commercial systems, where it was determined that darker-skinned women had error rates of up to 34.7%, while lighter-skinned men only had mistakes at the rate of 0.8%.
In addition, it found a higher composition of light skin tones, taking into account the Fitzpatrick classification, in the data systems of IJB-A (79.6%) and Adience (86.2%). From all this he concluded that gender classification systems required attention if commercial companies wished to build "genuinely fair, transparent and accountable facial analysis algorithms."
























Leave your comment