International. According to Oswaldo Palacios, senior account executive in Mexico and NOLA at Guardicore, a company that is part of Akamai, the demands of cybercriminals are growing proportionally with the increase in ransomware attacks, with an average cost for the ransom of the information of 84 thousand dollars.
The most painful thing about these charges, in addition to the obvious fiscal detriment and that imply liquidity for those who commit crimes, is that they go hand in hand with an excessive increase in attacks of this type. According to the World Economic Forum's most recent report, WEF The Global Risk Report 2022, ransomware increased by 435% in 2020. In addition, the value of crypto-assets received as payments to rescue information was quadrupled, taking into account crypto payment addresses that have already been identified as being used for these purposes.
As can be detailed below, in Figure 3.1 of the aforementioned report, the total in millions of dollars of cryptocurrency value received in 2020, in addresses identified for ransomware payment, reached 406.34, which translates into an increase of 437.21% compared to 2019.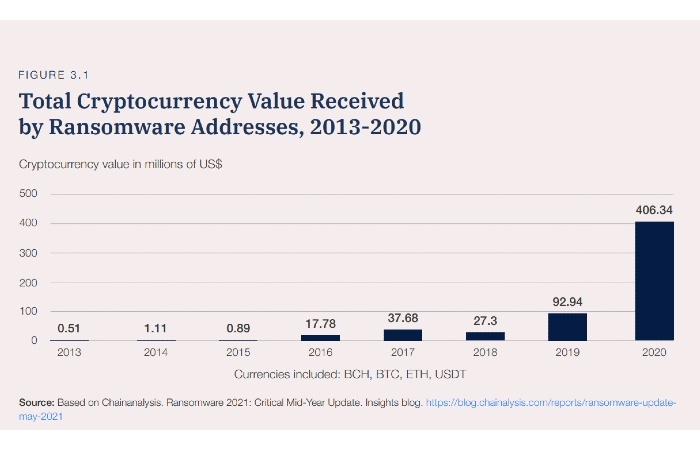
Apart from this data, the document notes that 85% of the World Economic Forum's Leading Cybersecurity Community maintains that ransomware is becoming a threat "that grows dangerously and represents a major concern for public safety." It also considers that the sophisticated cyber tools we currently have "also allow cyber threat actors to attack their selected targets more efficiently" so that they should not settle for opportunity-based targets, a matter that demonstrates the high potential for targeted attacks, which can lead to greater financial damage, but also social and reputational in the future.
What should you consider in a ransomware attack?
In that sense, Palacios states that there are several parameters to measure the impact of ransomware, but the most relevant corresponds to the question of how much money would I lose per minute, hour or day if my computer systems stop working? Considering that transactional and billing portals, among others, can be considered critical applications.
Another parameter to consider is the time it would take your company to restore the operation of its systems, or the cost of implementing a disaster recovery system, which may include alternate sites, staff training programs, and backup systems.
The case of the American provider CompuCom stands out, which confirmed (in March 2021) that it expected to lose up to 8 million dollars in revenue due to the temporary suspension of certain services after the DarkSide ransomware attack, in which the colonial pipeline company was attacked. To this figure he added a total anticipated expenditure of 20 million dollars to restore his services and address other problems remaining from the attack.
For Palacios, despite the fact that experts recommend not paying a ransom demanded by cybercrime, some companies pay the ransom fees in full, but do not receive the means to reverse the encryption of their data, so, in those specific cases, organizations spend a lot of time and money to rebuild what was lost.
Possible measures to avoid paying for ransomware
Palacios believes that since the average ransomware incident lasts 16.2 days, creating a defense strategy that prevents lateral movement at the beginning of an attack can help prevent widespread data loss, high costs, and downtime if the worst were to occur. He adds that, some attackers may exfiltrate sensitive materials to sell or exploit.
Once a ransomware attack is discovered in an IT environment, Palacios recommends that security leaders should ensure that there are no more infected assets, which can be achieved with a visibility tool at the level of the communication process within a server, in this way the activation of the malware will be neutralized and it will be known exactly where it is. "Another important point is that it cannot be propagated in the network, something fundamental so that this does not happen is to have a microsegmentation tool that allows isolating the critical assets of the company."

The expert believes that a strategy to prevent new ransomware attacks is to have visibility and segmentation at the process level in servers or assets, inside and outside the data center. "We can't protect what we can't see." Thus, it states that the answer is to create a whitelist of communications processes, to know when an infected asset tries to communicate with the controller server and block said request. "This will be proactively mitigating the threat."
Finally, Palacios indicates that planning a ransomware mitigation and defense strategy must begin long before an organization is affected. This is possible by using network segmentation policies, which allow organizations to block common ransomware propagation techniques. Oswaldo concludes that using zero-trust microperimeters around critical applications, backups, file servers and databases, coupled with creating segmentation policies that restrict traffic between users, applications and devices, will drastically reduce the attack surface.

























Leave your comment